Description
Validates session information. This API is designed to be called by Windows applications running from within Cameyo's session, in order to securely validate session information such as the user's email.
Syntax
https://api.cameyo.com/tokens/[tokenId]/validate?tokenKey=...&ttl=...&userId=...
Required parameters
•tokenId: token ID. This can be obtained from the session's environment variable RAP_TOKENID.
•tokenKey: token key. This can be obtained from the session's environment variable RAP_TOKENKEY.
Optional parameters
•ttl: number of seconds following session's creation, after which the API should fail. For example if this is set to 300 seconds, then the API call will fail if called 301 seconds after the session was created. This allows the calling application to ensure that the token being passed is that of a freshly-started session.
•userId: user's email as specified in environment variable USER_ID. If this parameter is specified and is different from the actual session's authenticated user, the function will return 403 forbidden.
Return
200: success.
400: invalid parameters.
401: invalid token key, or expired.
403: the specified information (i.e. userId) is not correct, and the application should consider it invalid.
404: token not found.
500: an internal error has occurred.
Example
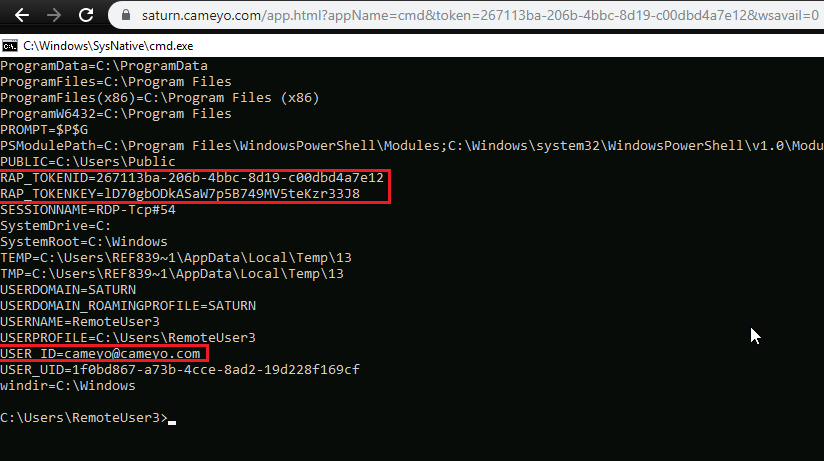
During a Cameyo session, your application can read session and user information from environment variables. To ensure that an environment variable hasn't been forged by a malicious user, here we will show how to validate a Cameyo environment variable. In our example we will validate Cameyo's USER_ID environment variable by calling https://api.cameyo.com/tokens/RAP_TOKENID/validate?tokenKey=RAP_TOKENKEY&ttl=180&userId=USER_ID
Bold keywords are to be replaced by their equivalent environment variables. When your application calls this Web API, it will receive HTTP 200 success code if the three elements match (session ID - session key - user ID), or an error code if they are incorrect / forged. Note that the ttl parameter limits the validity of this API to X number of seconds following the session's start (in this case 180 seconds), which provides extra security to ensure that this API isn't used outside of a session's starting time frame.
Example below:
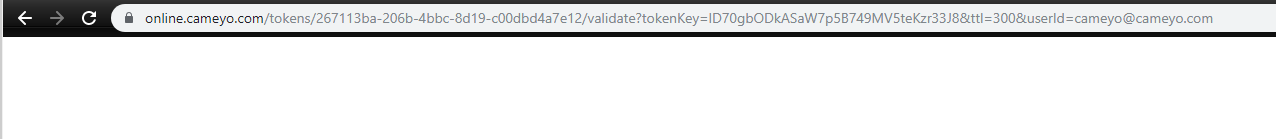
Example with a valid user ID:
https://api.cameyo.com/tokens/267113ba-206b-4bbc-8d19-c00dbd4a7e12/validate?tokenKey=lD70gbODkASaW7p5B749MV5teKzr33J8&ttl=180&userId=cameyo@cameyo.com
=> 200 success:
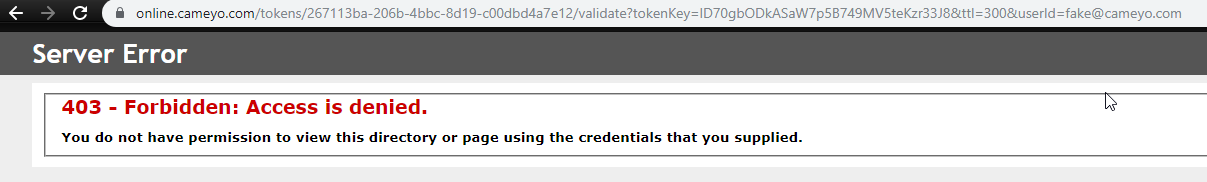
Example with an invalid user ID:
https://api.cameyo.com/tokens/267113ba-206b-4bbc-8d19-c00dbd4a7e12/validate?tokenKey=lD70gbODkASaW7p5B749MV5teKzr33J8&ttl=300&userId=fake@cameyo.com
=> 403 forbidden: